Originally Published March 28, 2022
On March 25th, a Friday just past the regular 9–5 employee working hours would be over at Twitter Support, I was finally after working on this project for over a month, inauthentically reported off of Twitter by the single target multi-account hate operation dubbed KassandraSeven.
Before we do the post mortem analysis, let’s talk about a few things.
Throughout this operation I have been straightforward and honest the whole time, kept a respectful tone, didn’t harass and did nothing that would warrant a legitimate action against my account. I used my own name, pictures, family, experiences, video, email, operated just one account and used only materials deemed allowable under fair use policy, or in one case I requested and received permission.
Mensch gets it. Susan who likely gave up her full identity to not only Jim, but to anyone who cares to dig with another boneheaded simpleton error of talking when silence is needed, doesn’t. I was sitting in carpool waiting to pick up two of my kids when those juicy details solving the final pieces of the puzzle, unsolicited by me might I add, came through buzzing hot via direct message on my phone. Jim when asked via LinkedIn regarding the name, as he should, would neither deny nor confirm.
For the time being I am content with withholding that information in confidence until it’s required by a matter of law or necessity. Same likely with Jim and others including my contact.
My suggestion to Sue and anyone within the org who is smart enough to realize it, is consult your lawyers, then meet with authorities before it is they whom decide to meet with you. Walls are closing in. Secrets don’t stay buried, and as Sue said on Twitter, the internet is forever, at least in the sense that federal prosecutors who have greater investigative authority are concerned. I will be answering SlimJimWatkins, whom I always suspected as a Fredrick Brennan sock, question in due time. Or a federal investigator will. All I do is kick the hornet nests and see what happens. And man, did the hornets buzz.
As an adult, I rarely if ever get mad, the one genuine emotion that I have had to fake/pretend to be at times, to convey a message because it’s a mostly foreign concept. That is why the weaponized attacks that these thugs use had no effect requiring them to get creative and increasingly sloppy during their operation against my accounts on Twitter and Medium. Seriously, when I had a gun pointed to my head briefly on one occasion, the emotion I expressed was annoyance as that was delaying me from getting to my destination. I kept my car, no one was hurt and we both went our separate ways, me annoyed, but not angry. That is how my mom raised me, to be respectful, cool-headed, and kind.
Always pull from your own real world experiences as Louise above suggests. You’ll be caught otherwise. I guess my real world experiences seem unreal to people that live/work 24/7 to attack, harass and encourage others to self-harm or undertake criminal behavior.
This isn’t my first rodeo folks. Probably won’t be my last.
One job I took years ago, using a company message board posting again, as myself, to start a serious discussion, ask questions, get answers from others who defended the target who was embezzling and gambling off high six-figure earnings on the weekends in Wendover, on Craps no less, and have those documented by the company resulted in an epic thread. Most of the discussion I pointedly asked questions and got his defenders to address and agree with all my points on how he mismanaged his franchise, citing known operational facts. People can’t defeat facts, despite willingness to just step over and ignore a cold body of evidence, hoping nobody will notice.
When I was finished, never revealing that he sent a thug, twice my size at me on the streets whom I recognized by sight but not by name, to threaten me ending instead in a smile and handshake after conversing, I told the company moderators that I was finished documenting my complaints, asked them to close out and save the thread. Less than three minutes later that happened.
He of course lost his job.
I expected going into this bigger operation that I would get a flood of emails, letters in the mail and phone calls, data that would prove useful to my underlying goals. That is what these single purpose hate account operations do when they are functioning correctly. They find personal information, amplify psychological attacks, make threats, blackmail, encourage suicide, illegal activity or death.
None came.
In other past similar work (who works just one gig these days anyway), I had plenty of calls and emails including having a surprise Federally approved wire-tap recorded conversation with one client, that Discovery turned up a heavily likely classified redacted copy of. As we were both aware that our conversation wasn’t private, I asked one question after a short pause and a chuckle regarding known felonies that that company, a federal contractor, had committed. My contact, knowing how useful the situation was, obliged.
They settled.
Surprised that all these operatives found was my fairly recently created LinkedIn profile, which I only provided details on for work I have done that I wanted to share professionally with others.
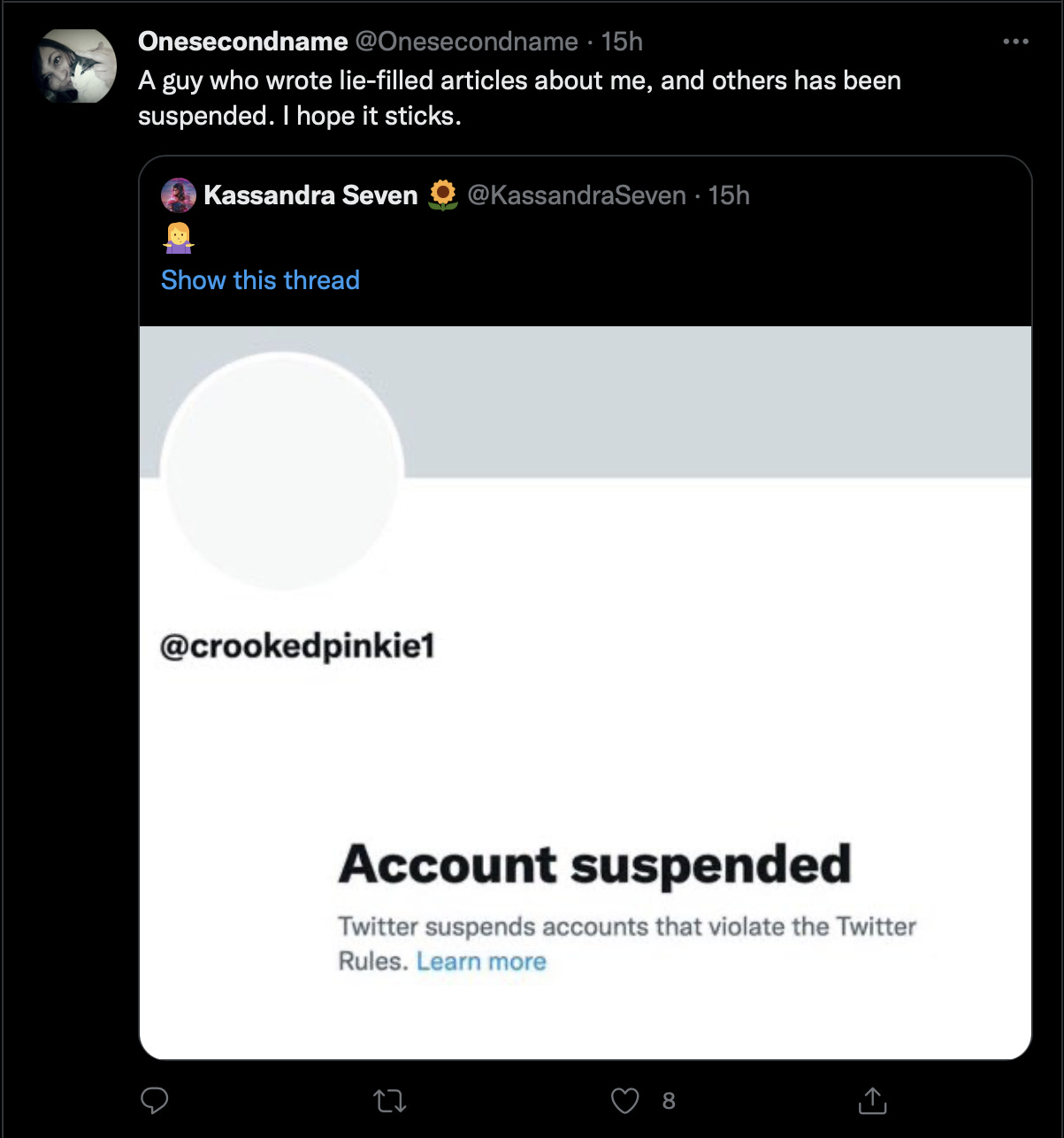
I have dutifully reported, rather than tattled, something I always asked younger children when they came up to me at recess regarding a complaint. I asked that fundamental question of one of the associated accounts within this likely criminal nexus, onesecondname, during the first set of our interactions where she later threatened to call up parents of students I worked with and KassandraSeven my employer then posting my work history. She of course wouldn’t answer it.
It is reporting when someone could be harmed, is illegal, or dangerous. The KassandraSeven single purpose, multi-account hate network fits that bill precisely.
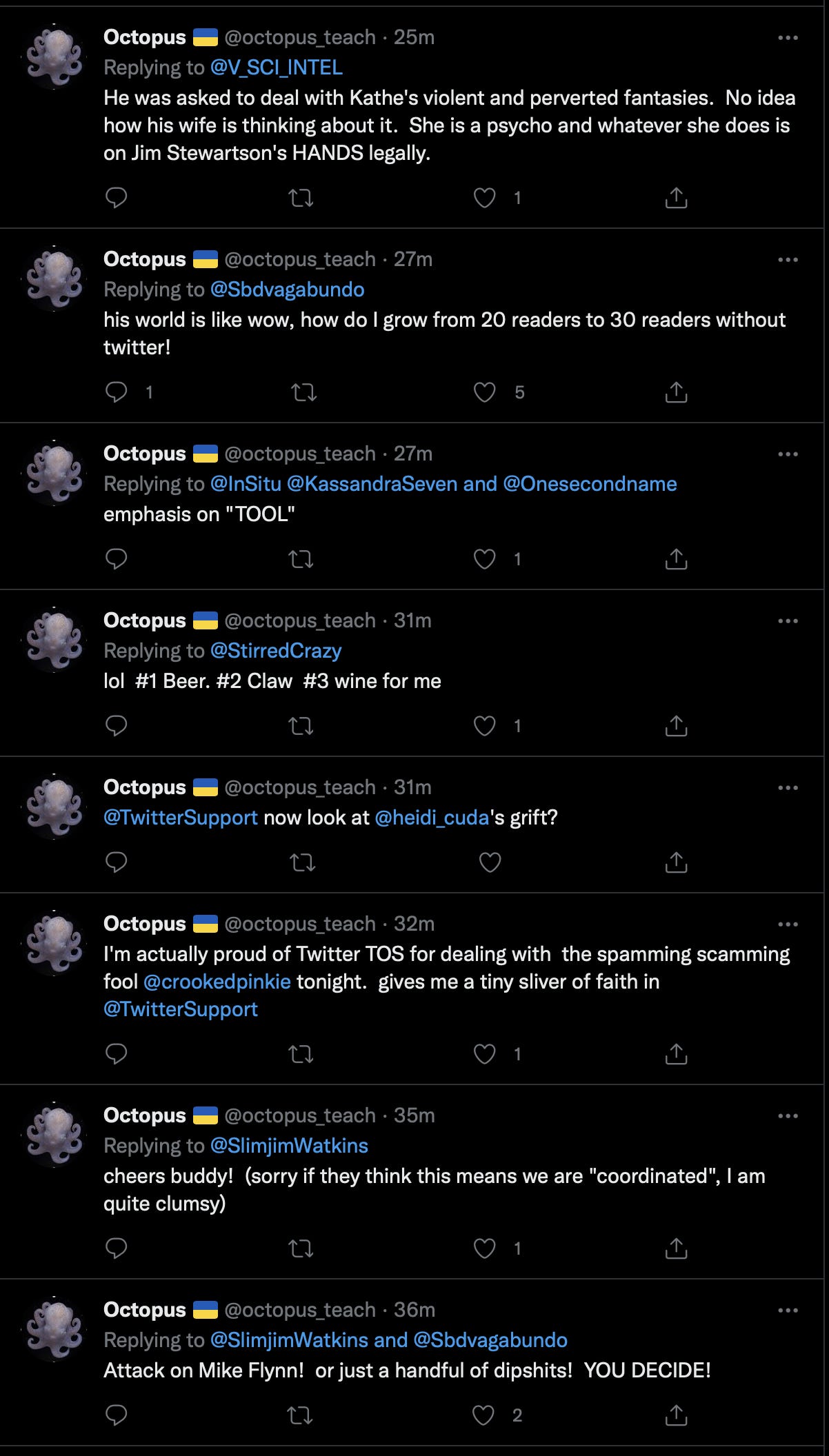
Spiral Dee has good reason to worry, not about Jim or I, but what operations other members have undertaken and accomplished in the past may or may not get dug up fully. Those potential crimes, can be charged to all or some members involved in a criminal conspiracy depending on how prosecutors establish the evidence given before a grand jury.
I have no concerns over my work, nor the ability to continue to find new work because like Sue says, people don’t like hiring bold-faced liars, something she may find easier doing than say having a criminal record.

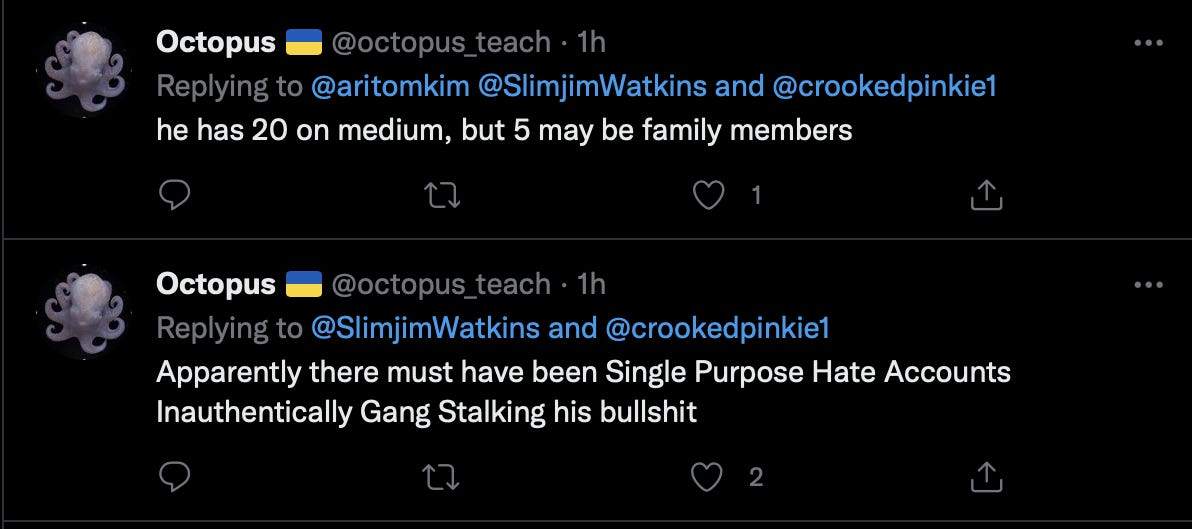
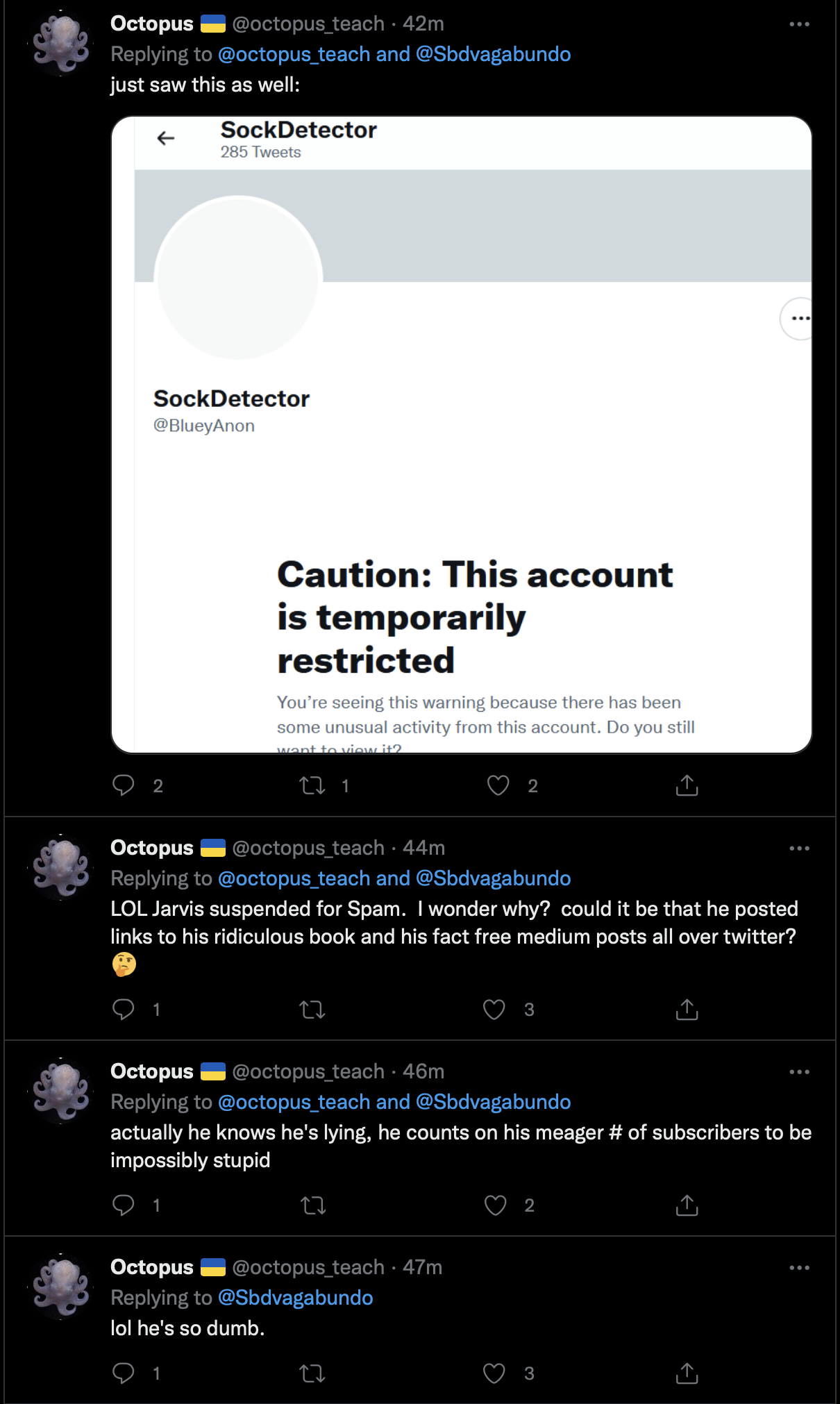
As I mentioned before, I thinned the herd of sock, recycler and probable bot accounts before I engaged the third time to make it harder for them to accomplish an account takedown. All three of these accounts, possibly sock-burner accounts connected to larger fake-left accounts. These small accounts do more of the malignant coordinated attacks on behalf of the organization, knowing that these are more likely to get suspended, while rarely using the boss level, Fredrick, Susan, Chad, Louise and Mike accounts they do not want to lose. Sock-burner accounts are generally the ones used more aggressively skirting Twitter TOS and safety.
Let’s get to the main event, the Post Mortum.
Here below is the one visible assigned attack tag, made within Twitter, and employing the same operational negative social influence wedge strategy I documented previously with Sue’s behavior.
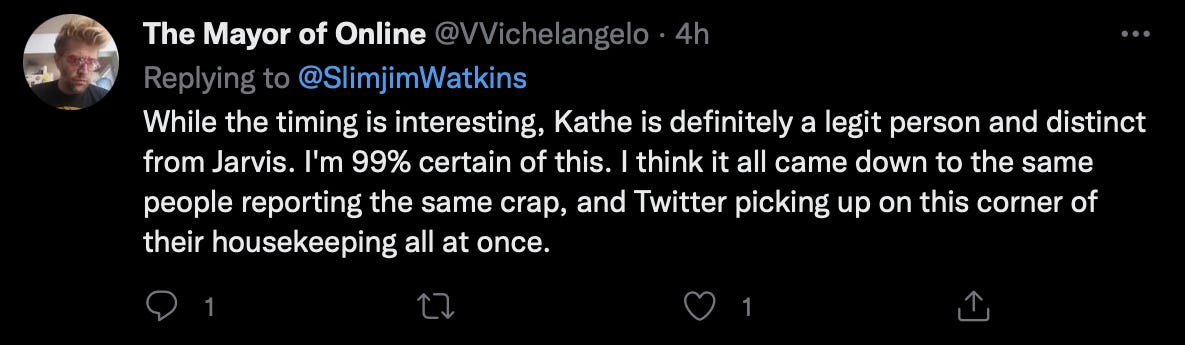
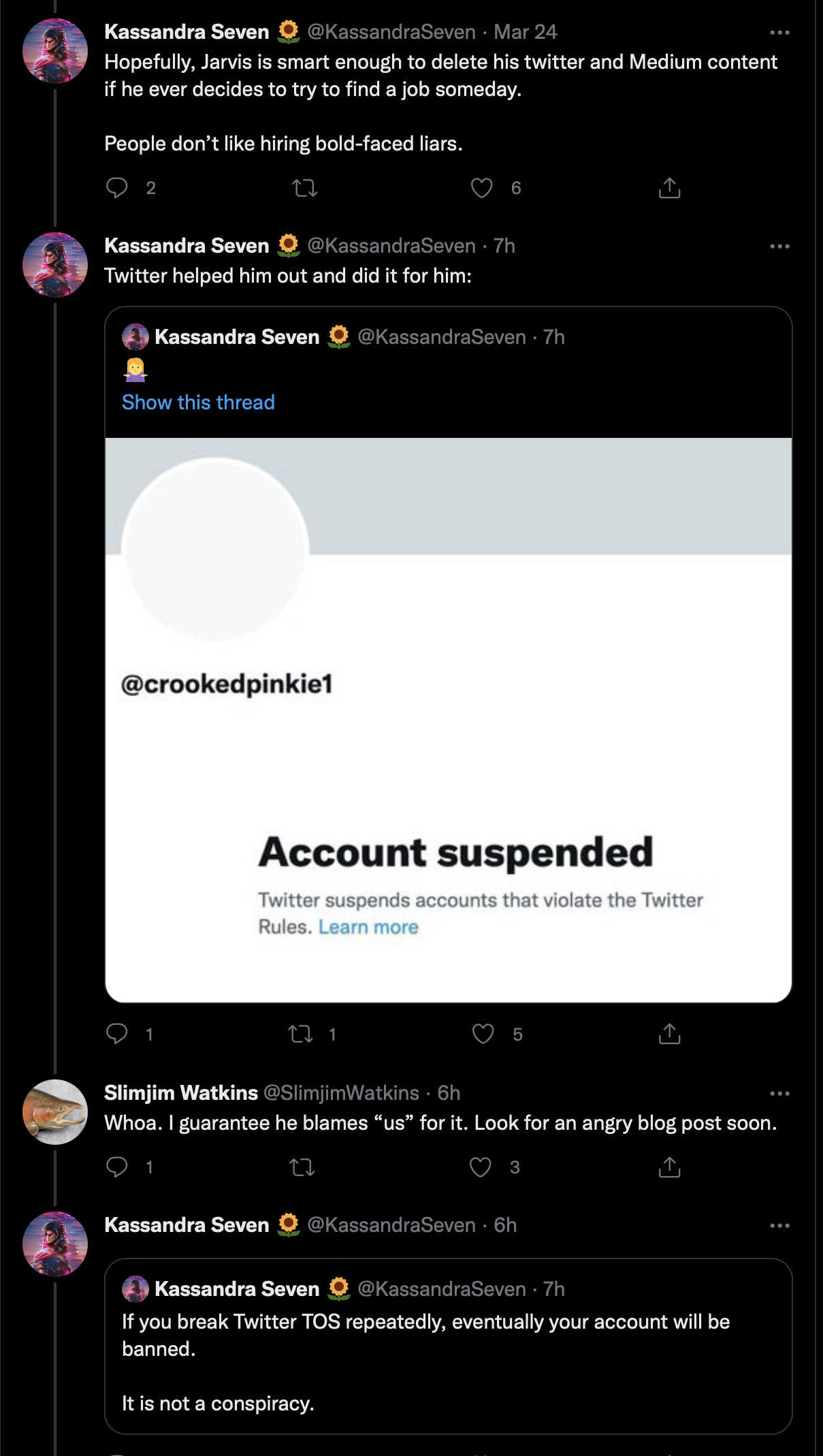
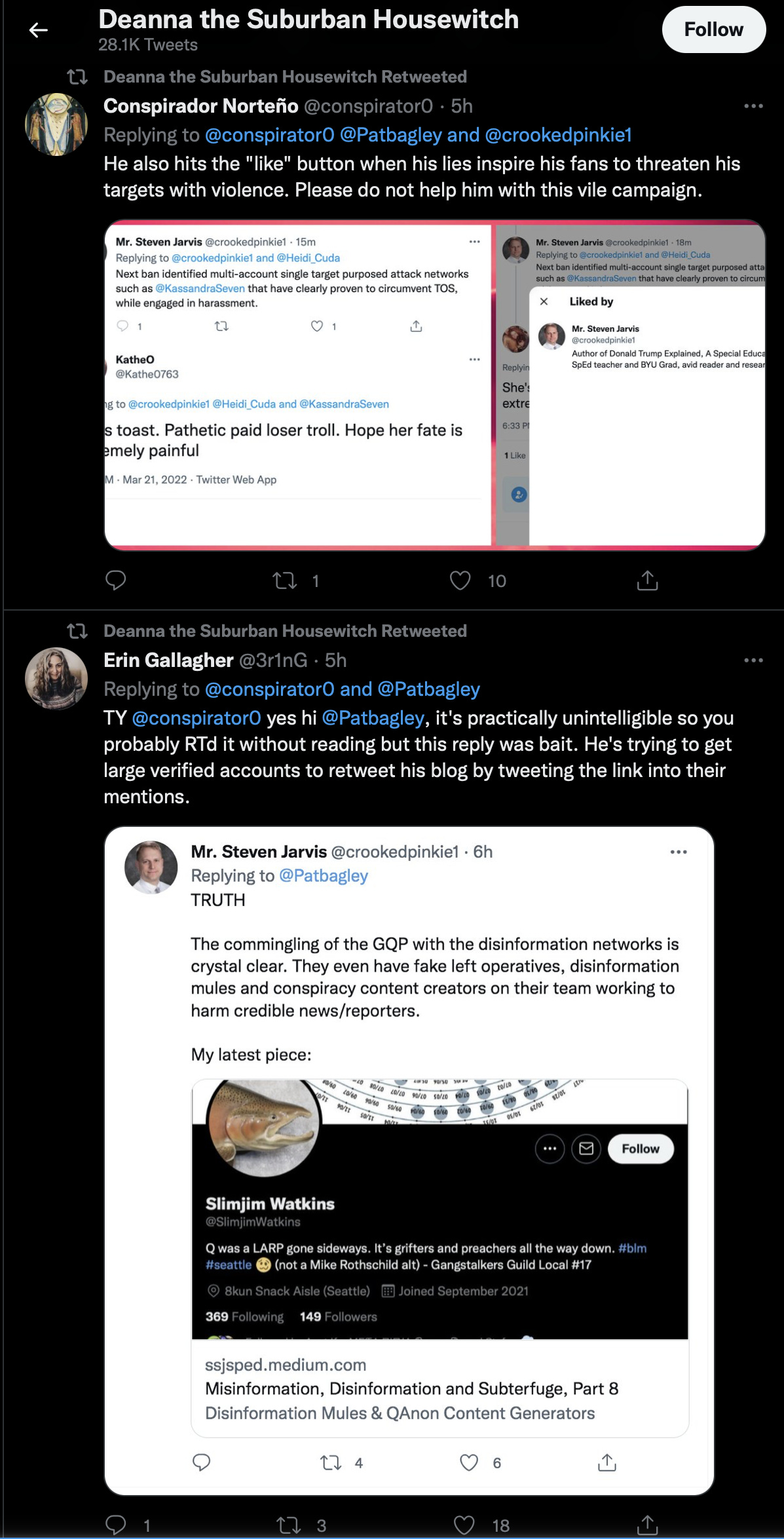
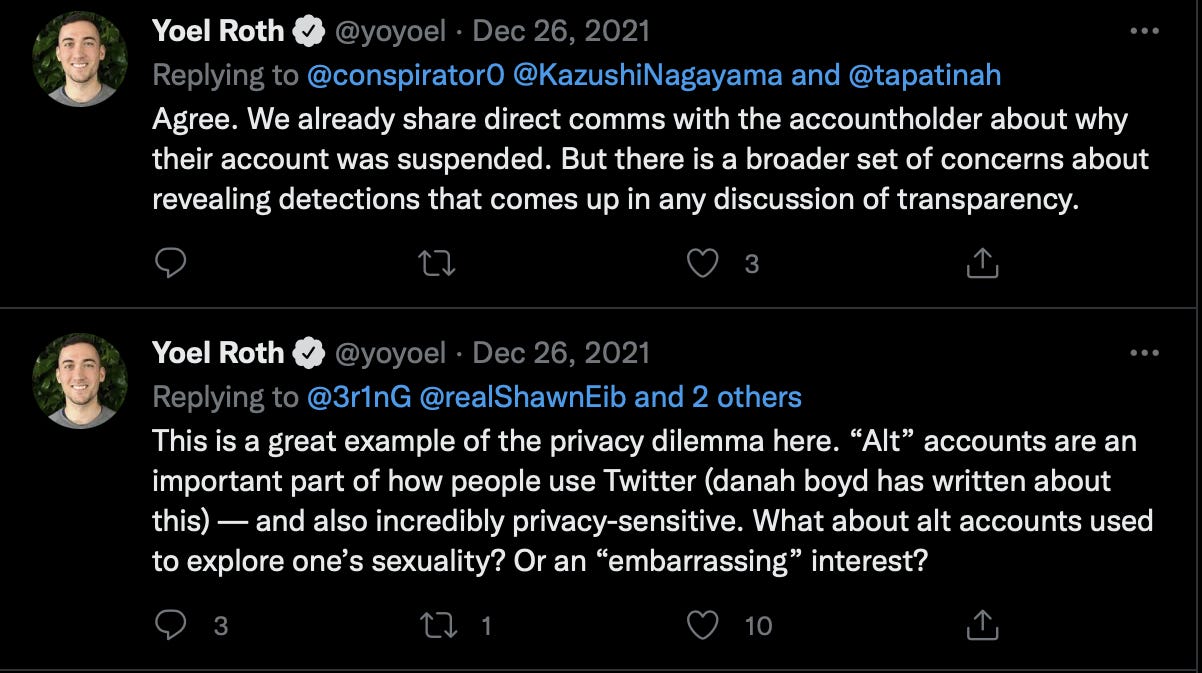
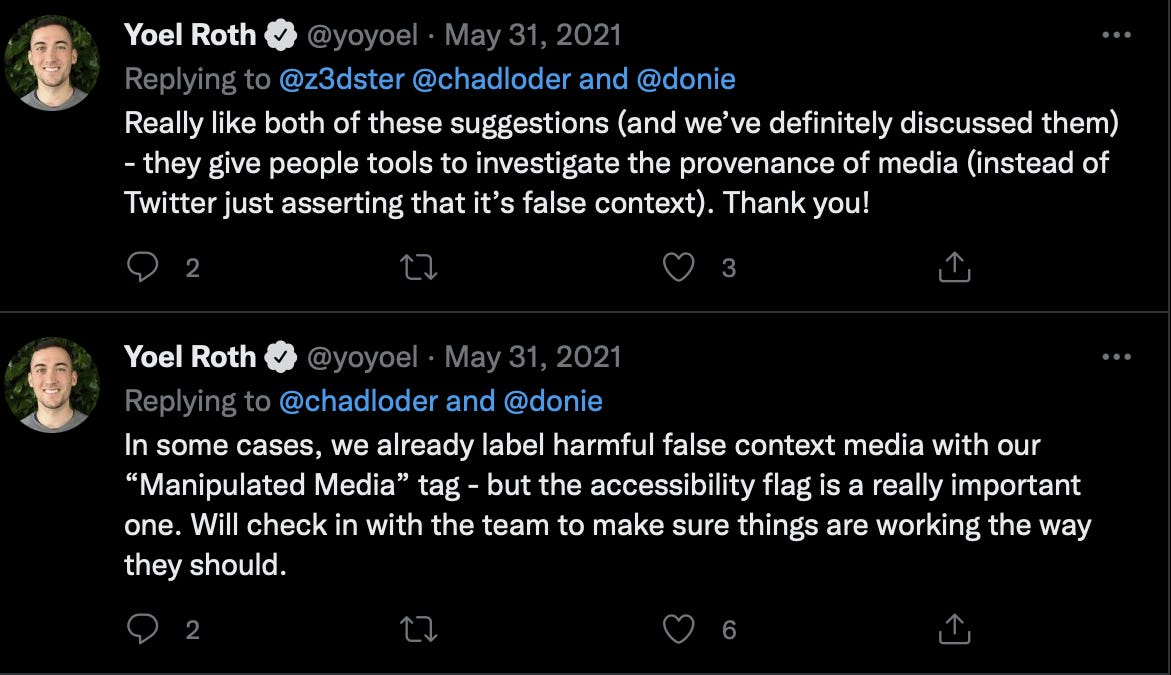
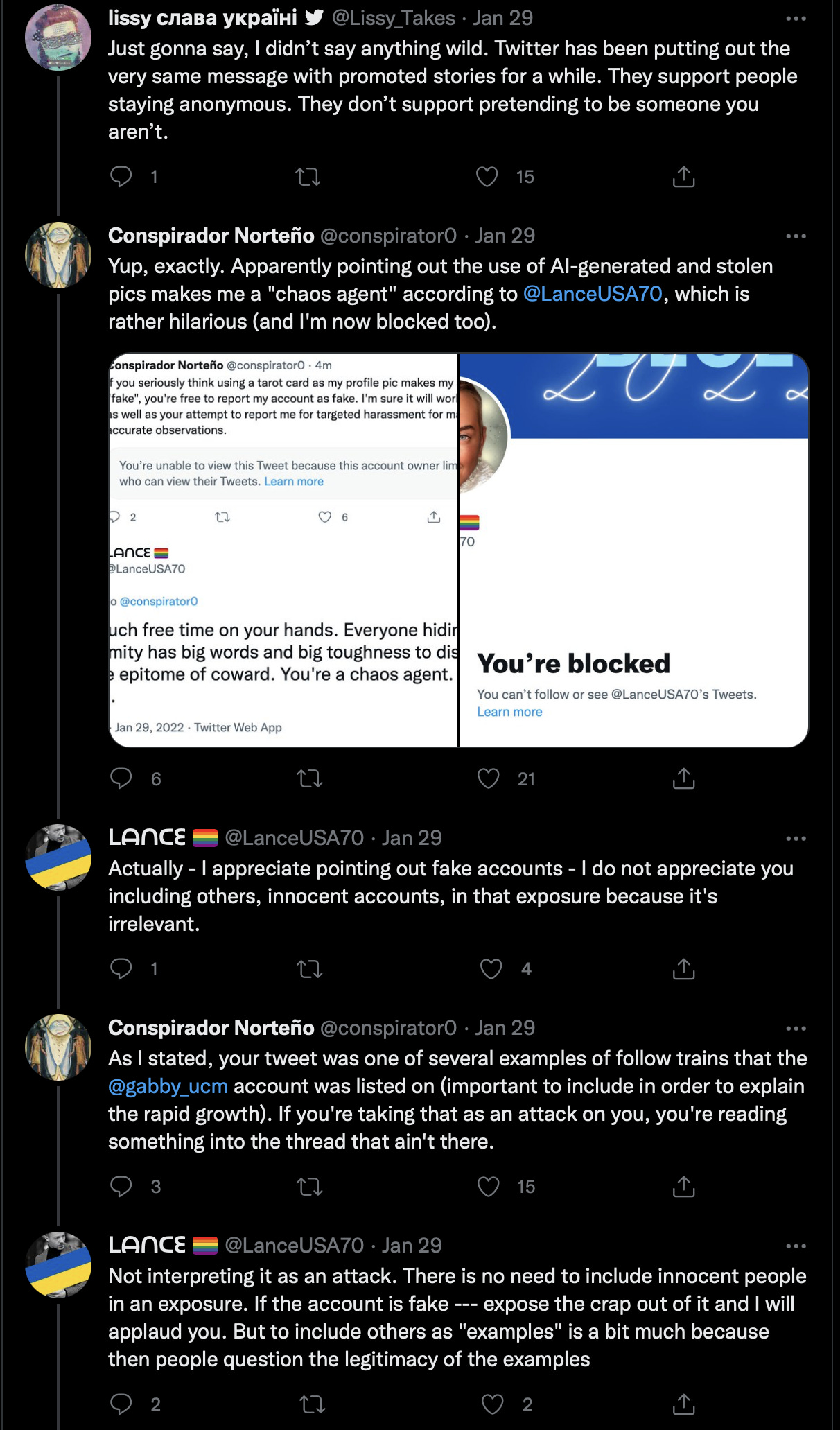
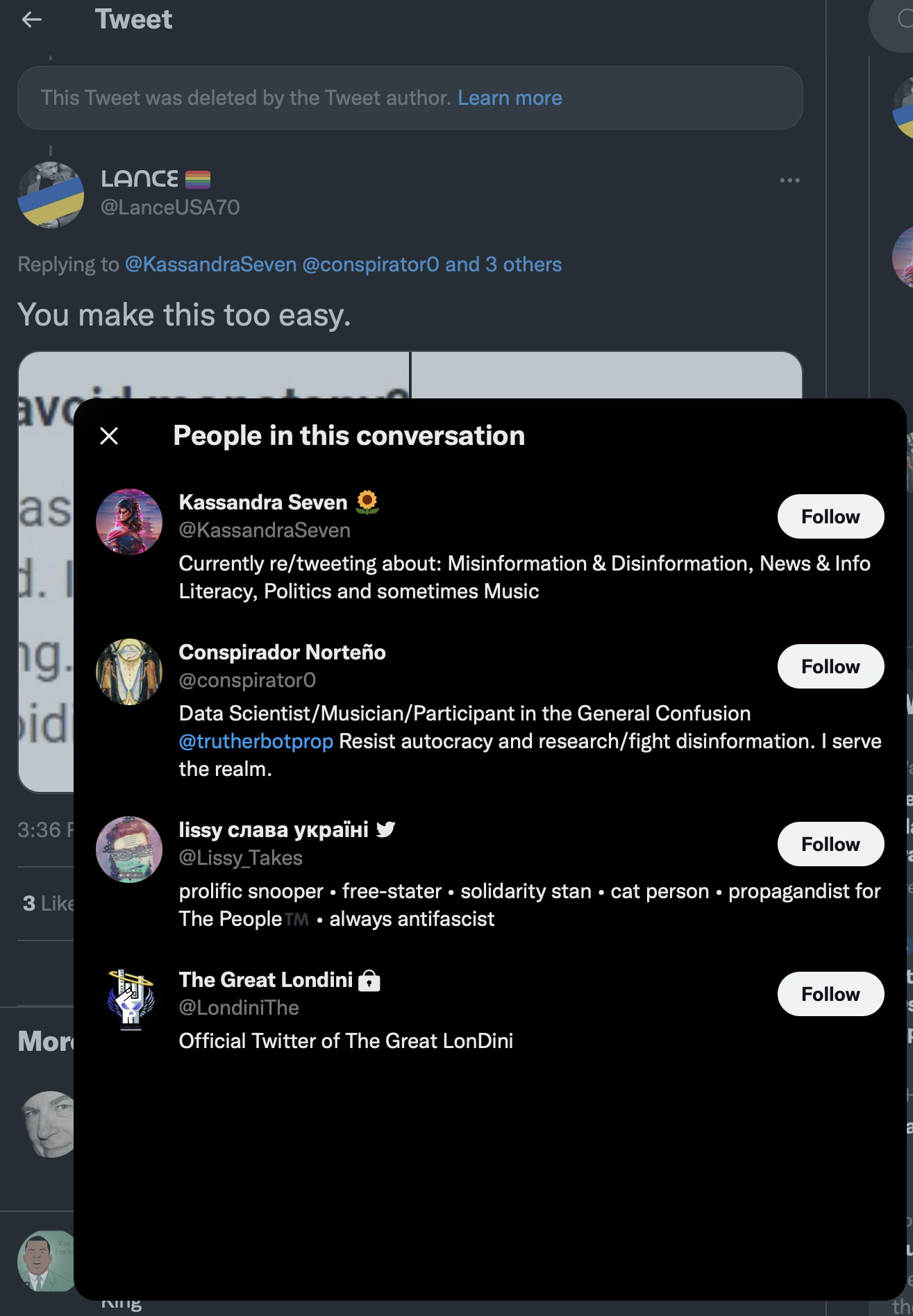
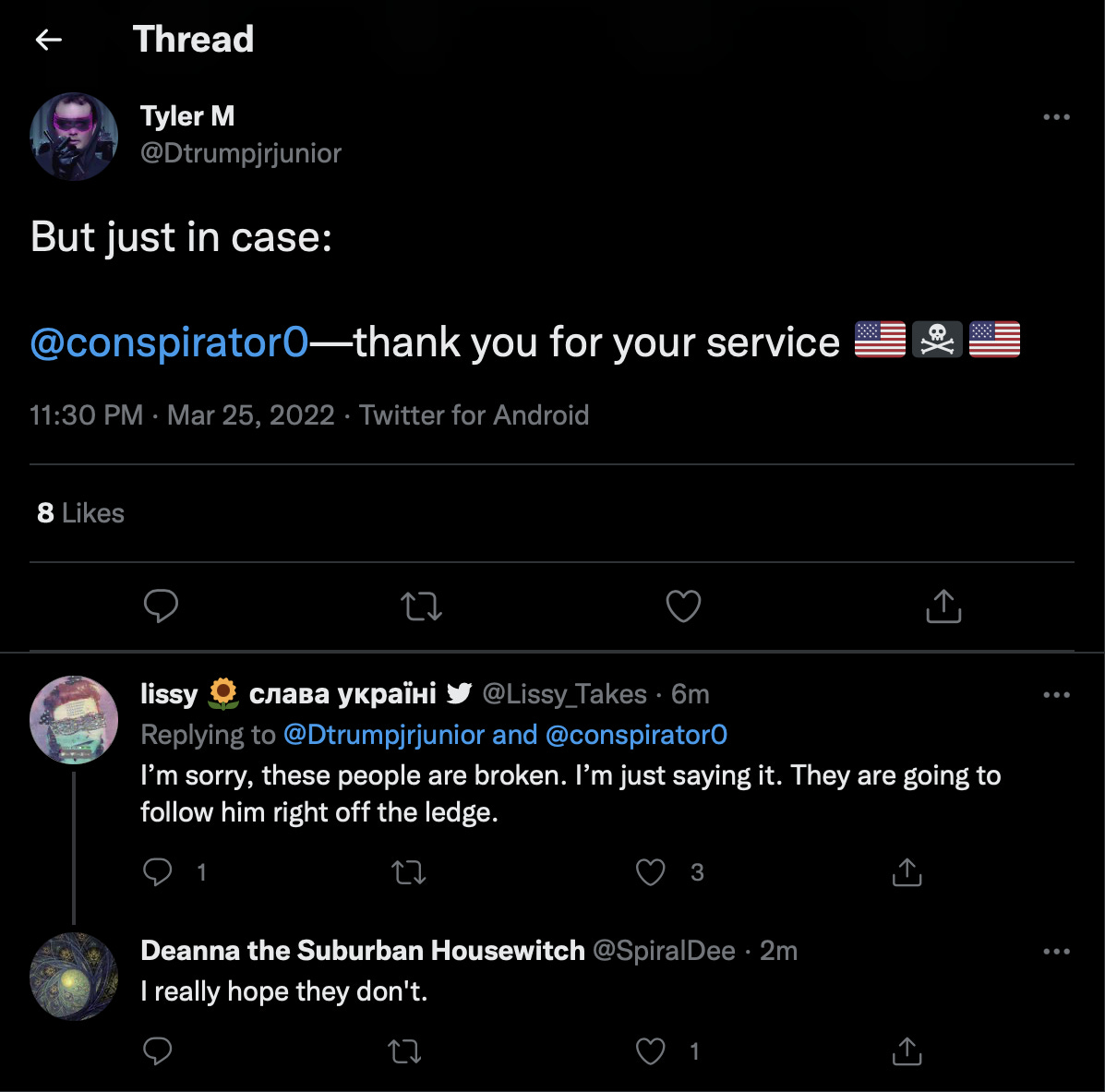
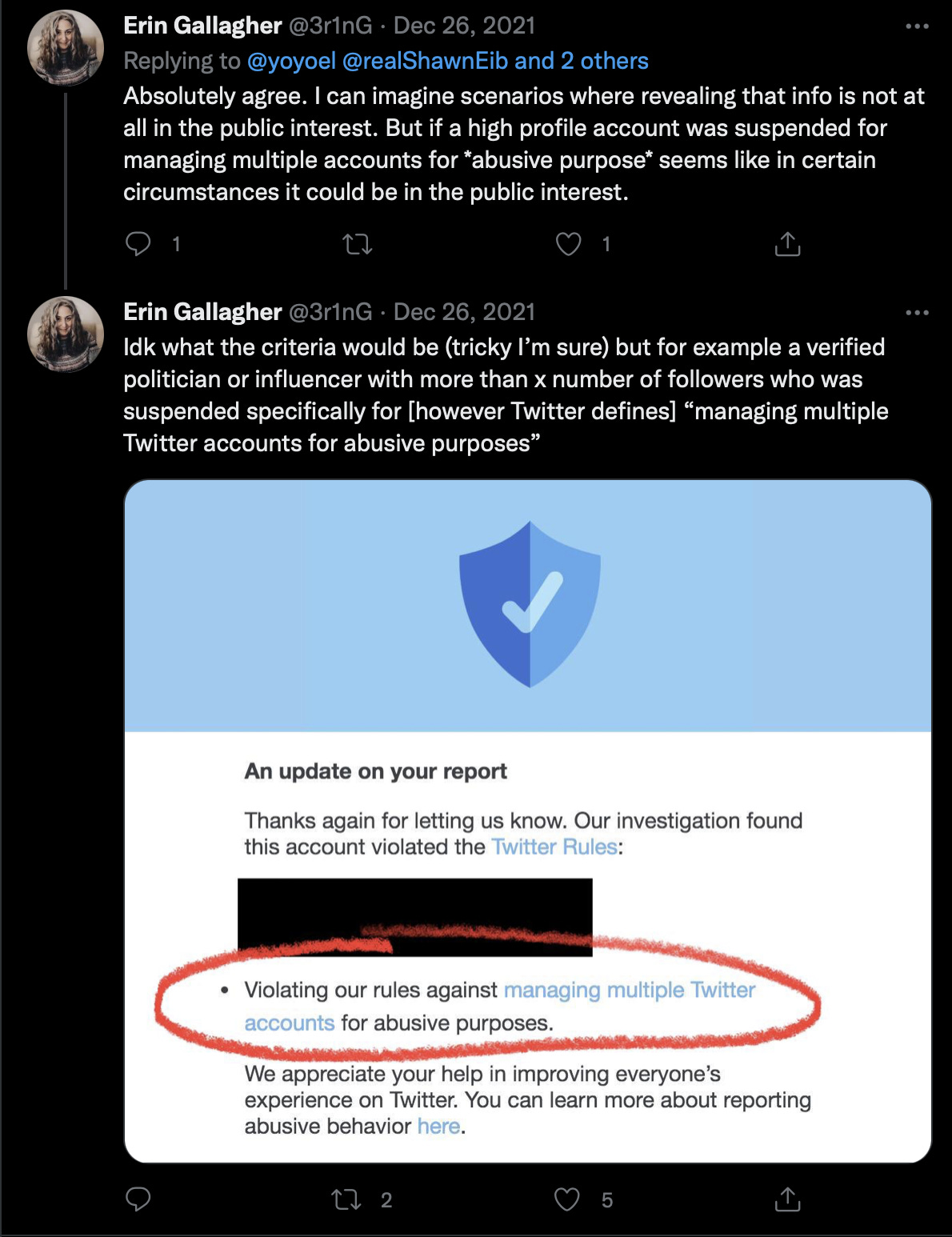
Two of the same malignant mid-sized accounts within their false researchers base, conspirator0 and 3r1nG who uses the name Erin Gallagher, were again deployed for the takedown. Based on 3:58 PM time stamp and the email I received from Twitter notifying me of the suspension, 5:08 PM this was likely at the start of their collective inauthentic work activity to attack my account.
What the aligned accounts did next, probably mass reported five of my tweets made over the course of one full day including the one I sent in response to a mutual follow, Deseret News’s and longest in the nation resident political cartoonist Pat Bagley.
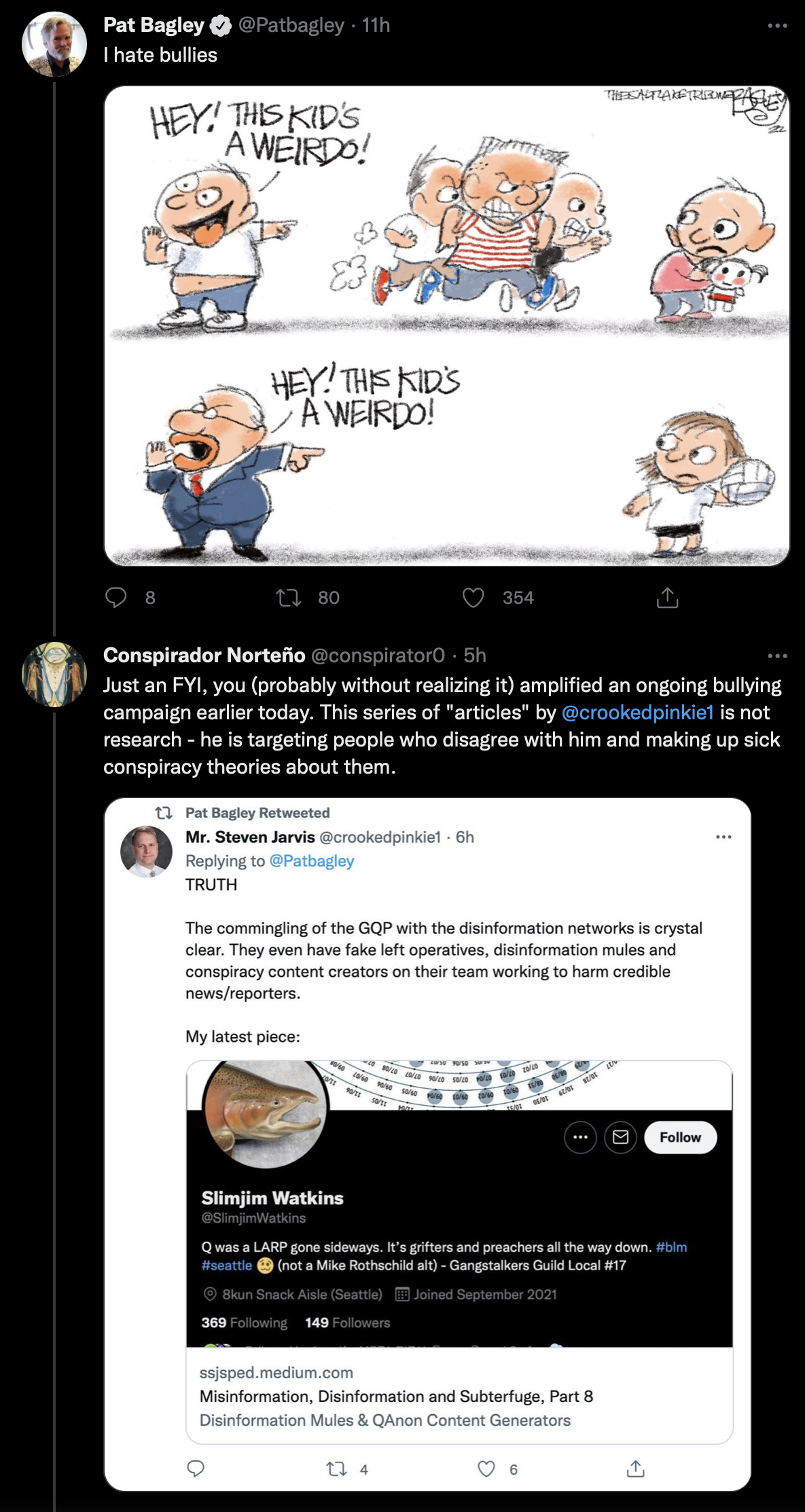
I would also assume, based on comments by members of the organization, they marked my responses to both Eric Garland and Seth Abramson whom showed up in my last column, then manipulated Twitter’s reporting system via automated bot activity or used an inside man. Along with my pinned thread, response to Pat Bagley I had a response to Don Winslow as well. That makes five. Other than Mr. Bagley, the other accounts I responded to are high value targets of their operations, being prominent verified accounts that actively work opposite of their fifth column aligned agenda their team is on.
Spamming, is sending out the same message countless times within a short period of time. My single tweet response to Winslow, Abramson, and Garland were appropriate, differentiated, and connected in a manner to the original post. In order for those actions to be described as spam, they would have had to be duplicated, multiple times. Pat Bagley was the only account they engaged using the negative social influence attack because the other three accounts are fully on their operational radar, and have been since the Mensch dividing people into teams on Twitter. For this reason, I do believe the team thought the attack was unlikely to succeed needing to push a prominent connected account away via bullying him into it.
I do think these likely criminals, and I am accurately describing them as such, will, because of the exposure of operatives like Sue, wind up facing serious consequences not on Twitter, but in real life. But I have to ask, do they think they have an ace in the hole here having used positive social influence to repurpose a Twitter insider unknowingly into a serviceable asset to do what they need to get done?
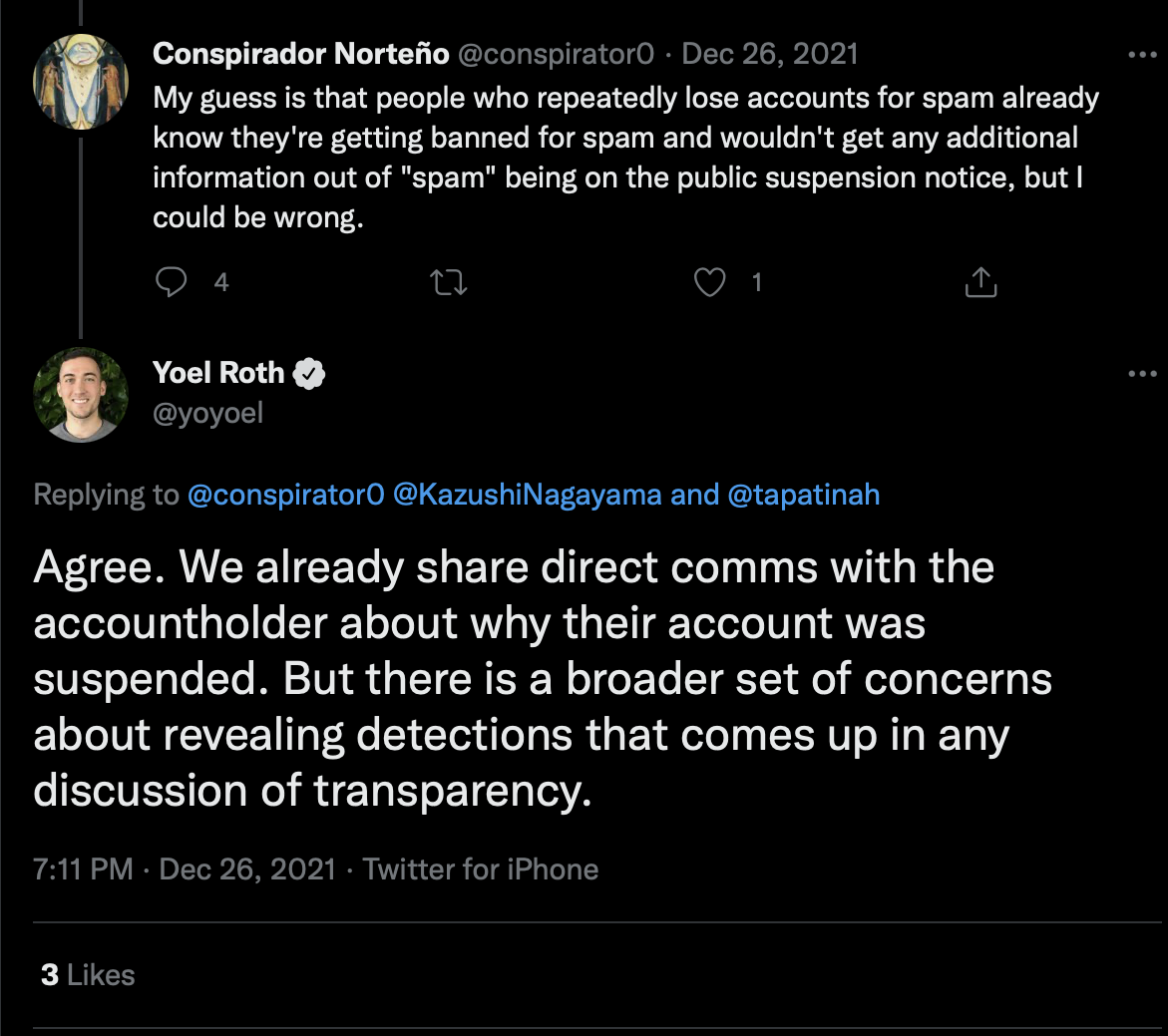
The account quoted here by Yoel Roth is the same account that demonstrated these tactics to remove both Jim Stewartson and my own account, that being Erin Gallagher. Conspirator0’s purpose was to show that Yoel Roth approves of Erin Gallagher’s work.
A positive social influence for Erin, a negative social influence for me.
Thank you conspirator0. Your service is duly noted.
It is highly interesting when the very author of the article posted above, has used the tactics she outlined to manipulate, earn trust, and inauthentically operate, breaking not just Twitter’s TOS on manipulation techniques, but likely federal laws that prevent using social media to do the very things she wrote on. Interesting indeed.
The inauthentic reporting tactic, claiming spamming, when possibly identifying five tweets that were dissimilar and uniquely written, raised multiple red flags.
One, skipping the short-term suspension process, implies an override or manual execution of a permanent ban by someone on the inside.
Two, there was no evidence of spamming or manipulation by myself and therefore nothing to report.
Three, the timing between conscriptor0 and Erin Gallagher’s social influence wedge attack on Mr. Bagley and then my ban, again show that these two operatives were responsible for manipulation of Twitter Safety and Yoel Roth.

By gaining undue positive social influence on Twitter insider Yoel Roth now likely used also on Jim Stewartson, similar to how other operatives within this fifth column worked their connections to best position themselves for effective gatekeeping, disinformation peddling, and flaunting TOS, it all makes sense. Yoel thinks he is doing right, helping an intelligence agent involved in a PsyOp accomplish her mission of taking down her target.
Inside man.
I do think Yoel is getting played, by the expert social influencer and chaos agent Erin Gallager. But other questions linger that he needs to answer regarding what members of the group asked him to do, and why he did so, in a very public manner.
We’ll hopefully get to that eventually.
It isn’t just Erin either.
Some of those lingering questions swirl around inaction and actions taken.
Fredrick Brennan, a key operative in the KassandraSeven network, who in this tweet thread below saying he never wants to operate a chan again, spends his day “serving” a permanent ban on Twitter for highly dangerous and potentially legally entangling behavior for everyone else. Epstein had some sort of similar deal it seems as Fred has with Twitter Safety. We all know what Epstein did with that opportunity. The same stuff he was doing before future Trump Cabinet Member Alex Acosta gave him a free pass.
So why is banned Fred Brennan on Twitter, Yoel?
More importantly, why is Twitter Safety allowing the same devastating gang-stalking tactics to be used non-stop by the KassandraSeven network, to target those reporting on disinformation that wound up costing a man his life?
Why is it that Twitter Safety hasn’t shut down any of the single purpose hate accounts reported on thus far by Jim Stewartson and others, and then sent a report to the Feds or local jurisdictions where these operatives live? Don’t they have a legal responsibility to do so, or will that require Congress acting?Is Twitter going to fix the problem?
It is pretty big.
Ongoing.
All day long.
Every day.
With Twitter Safety and Yoel Roth knowing, often linked in via handle when these operatives engage in a coordinated attack. Not a good look for a company. Not at all.
Gang-stalking, targeted harassment, lying openly about things, coordinated with each masked account playing a different role in each weaponized psychological attack, this needs to stop.
Here is what Twitter must do.
Reinstate accounts removed inauthentically, like mine Jim Stewartson and others.
Ban the KassandraSeven operatives, ALL of them, including the ones that got verified becoming disinformation mules, able to push Fifth Column disinformation like the “Putin has Parkinson’s” using the social influence model to mainstream that into the media. Preserve a record of all of their account’s activity, including deleted tweets.
Remove inactive accounts. Can’t tell you how many 2013 “follows” that had zero history interactions since I began working on this project, but it was very high.
Require every account to be authenticated via a phone number, used periodically to confirm including alts.
Remove the ability for an account that has blocked another account to interact hidden on that person’s thread or an indirect retweet of that person. All alts too.
Verified accounts need to identify WHY they are verified.
The ball, for the time being, is in Twitter’s court.